Win32/Upatre.BI - Part Two
Config- June 14, 2015
- reverse engineering
- malware analysis upatre
- no comments
- Format of Upatre's Configuration
- Introduction
- Port
- (Encrypted) Strings
- Decryption Keys
- Check Keys
- Network Targets
- 1st Field - C2 root directory
- 2nd Field - Server Name
- 3rd Field - Download Path
- 4rd Field - Key Index
- 6th Field - Another Exe Filename
- Purpose of Targets
- Observed Config Files
- Sample 0x7347d213
- Sample 0xbda3abd2
- Sample 0x95e79d9a
- Sample 0x457f0283
- Sample 0x105beb32
- Sample 0x8d00dfdc
- Sample 0x98b126f5
- Sample 0x07ea0d7c
- Sample 0x7422731b
- Sample 0x846cb698
For more information about the malware in this blog post see the Malpedia entry on Upatre.
- Part 1: Unpacking (June 10, 2015)
- Part 3: Main Loop (June 16, 2015)
- Part 4: Payload Format (June 20, 2015)
The first blog post of the series on Upatre showed how to unpack the malware. You can download the unpacked sample from malwr.com if you like to retrace my reversing steps.
This second part focuses on the configuration of Upatre. The first section presents the format of the data structures used to store configuration details, such as
- the executable name
- the C2 address, port, and root directory
- the urls that host the (encrypted) malware downloads
- the keys to decrypt and validate the downloaded content
The second section then employs a small IDA script to extract and format the configuration information of ten samples (including the unpacked one). All analysed samples use the same configuration format, but they use it in slightly different ways. For example, all Upatre samples decrypt downloaded content with a key from the configuration file, but the key-scheduling algorithm might be different. I list the differences in the overview, but elaborate on the details in the upcoming blog post on Upatre.
Format of Upatre’s Configuration
Introduction
As mentioned in part one, the unpacked code is position independent. All functions and global variable are accessed by a global offset table. This offset table is located at the start of the .text section. Upatre gets the absolute address of the offset table by rounding down the EIP — which it obtains by a fake call — to the page boundary. It then adds the six offsets (stored as WORDs) to the base address to obtain a table of absolute addresses:
.text:0040127A call $+5
.text:0040127F pop eax
.text:00401280 sub esp, 64h
.text:00401283 mov ebp, esp
.text:00401285 and ax, 0F000h
.text:00401289 add esp, 0FFFFFF7Ch
.text:0040128F push 6
.text:00401291 pop ecx
.text:00401292 push eax
.text:00401293 lea eax, [ebp+64h+global_address_table]
.text:00401296 pop esi
.text:00401297 mov edi, eax
.text:00401299 mov ebx, esi
.text:0040129B
.text:0040129B loc_40129B:
.text:0040129B xor eax, eax
.text:0040129D lodsw
.text:0040129F add eax, ebx
.text:004012A1 stosd
.text:004012A2 loop loc_40129B
The following table shows the six entries of the offset table. The address column shows the resulting absolute address given the .text section starts at 0x401000:
| row | offset | address | type | name |
|---|---|---|---|---|
| 0 | 1380h | 0x402380 | data | config |
| 2 | Ch | 0x40100C | subroutine | fetch_and_advance |
| 4 | 14h | 0x401014 | subroutine | decrypt_strings_and_get_os_infos |
| 6 | 138h | 0x401138 | subroutine | get_decrypted_string_by_index |
| 8 | 13Fh | 0x40113F | subroutine | get_field_of_target |
| 10 | 14Dh | 0x40114D | subroutine | send_user_infos |
The first row points to the configuration data. The routines fetch_and_advance, get_decrypted_strings and get_field_of_target are stubs to access the data structures. Half of the decrypt_strings_and_get_os_infos routine, namely the decryption part, is discussed in this post, the remaining half, as well as the routine send_user_infos, follow in the third part.
Upatre uses one large structure as its configuration — referenced by the first entry of the global offset table. The config information is read inside decrypt_strings_and_get_os_infos which reveals most of the format. The following illustration shows an overview of the config data structure with example values from the examined sample:
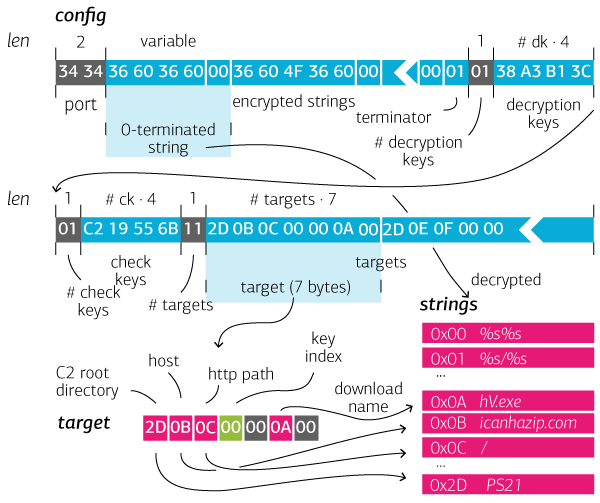
Port
The first two bytes of the config denote the lowest port address used in C2 communications. Each time the port referenced a random number of up to 3 is added, which results in a port range of four ports:
.text:00401786 FF 93 00 11 00 00 call [ebx+imports.GetTickCount]
.text:0040178C 83 E0 03 and eax, 3
.text:0040178F 03 45 C8 add eax, [ebp+64h+port]
(Encrypted) Strings
Starting at offset 0x2 the config contains a list of strings. Each string is zero-terminated. For example:
36 60 36 60 00 36 60 4F 36 60 00 7C 63 76 7D 00
Some samples store the strings in plaintext; my sample used the XOR key 0x13 to obfuscate the strings. The strings are first decrypted — if necessary — and then stored as Unicode in a newly allocated sections. The above list of encrypted strings, for instance, becomes:
25 00 73 00 25 00 73 00 00 00 25 00 73 00 5C 00 %.s.%.s...%.s.\.
25 00 73 00 00 00 6F 00 70 00 65 00 6E 00 00 00 %.s...o.p.e.n...
which represents the strings "%s%s", "%s%s" and “open”. Upatre also stores the pointers to the decrypted string in an array of pointers:
02854FE0 dd offset aSS ; *%s%s*
02854FE4 dd offset aSS_0 ; *%s\\%s*
02854FE8 dd offset aOpen ; *open*
...
The list of strings is terminated by byte 0x01, which is neither a printable ASCII character itself, nor decrypts to one. All above steps are performed by the following snippet.
.text:00401034 next_string:
.text:00401034 mov [ebx], edi
.text:00401036 add ebx, 4
.text:00401039
.text:00401039 next_letter:
.text:00401039 lodsb
.text:0040103A cmp al, 1
.text:0040103C jz short all_strings_done
.text:0040103E test al, al
.text:00401040 jz short loc_401044
.text:00401042 xor al, 13h
.text:00401044
.text:00401044 loc_401044:
.text:00401044 stosw
.text:00401046 inc ecx
.text:00401047 test al, al
.text:00401049 jnz short next_letter
.text:0040104B jmp short next_string
.text:0040104D ; ----------------------------------------
The following helper subroutine is used to get a decrypted string by an index passed in ecx:
.text:00401138 ; ecx = index
.text:00401138 ; Attributes: bp-based frame
.text:00401138
.text:00401138 get_decrypted_string_by_index proc near
.text:00401138
.text:00401138 decrypted_strings= dword ptr 60h
.text:00401138
.text:00401138 mov eax, [ebp+decrypted_strings]
.text:0040113B mov eax, [eax+ecx*4]
.text:0040113E retn
.text:0040113E get_decrypted_string_by_index
Some of the strings have a predefined purpose:
| index | example | meaning |
|---|---|---|
| 3 | text/* | first accept-type of the downloads |
| 4 | application/* | second accept-type of the downloads |
| 6 | Mozilla/5.0 (Windows NT 6.1; WOW64; rv:37.0) Gecko/20100101 Firefox/37.0 | user-agent |
| 7 | wevadez.exe | exe name of Upatre |
| 8 | LogE83.tmp | temp file used to store downloaded content |
The remaining strings are dull (like the format string %s%s), or referenced by the targets which are discussed later.
Decryption Keys
Upatre is mainly a downloader for other malware. The downloaded content, as will be shown in the fourth part of this blog series, is encrypted with a four byte key. The keys are stored in a variable sized array, with the number of elements indicated by one byte at the start of the array. For example, my samples stores one key:
.rdata:004025D9 db 1
.rdata:004025DA dd 3CB1A338h
Check Keys
Upatre also validates the decrypted downloads by comparing four bytes of the download to a second key. These keys are again stored in a variable sized array following the decryption keys, for example:
.rdata:004025DE db 1
.rdata:004025DF dd 6B5519C2h
Edit June 17, 2015: Some Upatre samples have no check keys. They use a simplified payload format, see the fourth part of this blog series.
Network Targets
After the two key arrays follows another array which contains information about the network targets. Each network target — except for the C2 server address — is represented by a 7 byte data structure (Edit: older samples use 6 bytes per target). Again a one byte value at the start denotes the size of the array, for example:
.rdata:004025E3 db 11h
.rdata:004025E4 target <2Dh, 0Bh, 0Ch, 0, 0, 0Ah, 0>
.rdata:004025EB target <2Dh, 0Dh, 0Eh, 0, 0, 0Ah, 0>
.rdata:004025F2 target <2Dh, 0Fh, 10h, 0, 0, 0Ah, 0>
.rdata:004025F9 target <2Dh, 11h, 12h, 0, 0, 0Ah, 0>
.rdata:00402600 target <2Dh, 13h, 14h, 0, 0, 0Ah, 0>
Upatre uses the following slim subroutine to access fields of a specific target:
.text:0040113F get_field_of_target
.text:0040113F
.text:0040113F targets= dword ptr -80h
.text:0040113F var_1C= dword ptr -1Ch
.text:0040113F
.text:0040113F movzx ecx, ah
.text:00401142 xor ah, ah
.text:00401144 add ecx, [ebp+64h+targets]
.text:00401147 mov eax, [ecx+eax*8]
.text:0040114A xor ecx, ecx
.text:0040114C retn
.text:0040114C get_field_of_target
The subroutine has two arguments: the target number passed in register al, and the desired field in ah. The subroutine returns four consecutive fields in register eax. Of this return value sometimes al is used, in this case argument ah corresponds to the retrieved field index. In other cases ah is accessed, which means for argument ah the field ah + 1 is accessed. By looking at all calls to the get_field_of_target-subroutine, one can quickly find out the purpose of most fields.
1st Field - C2 root directory
The first field of a target is needed when the target is used as C2 callback, i.e., as a receiver for user information. In those cases the first value of the first field serves as the index into the array of decrypted strings:
.text:00401158 mov edi, [ebp+64h+path]
.text:0040115B push '/'
.text:0040115D pop eax
.text:0040115E stosw
.text:00401160 mov eax, [ebp+64h+ip_nr]
.text:00401163 call [ebp+64h+get_field_of_target]
.text:00401166 movzx ecx, al
.text:00401169 call [ebp+64h+get_decrypted_strings]
...
(string is copied to path)
The referenced string is used as the root directory of HTTP GET requests to the C2 host (the details follow in the third part of this blog series).
2nd Field - Server Name
Here is an example where a target’s second field is referenced:
.text:0040163B mov eax, ecx ; tar_nr
.text:0040163D call [ebp+64h+get_field_of_target]
.text:00401640 mov cl, ah
.text:00401642 call [ebp+64h+get_decrypted_string_by_index]
.text:00401645 push eax
.text:00401646 push [ebp+64h+hInternetOpenHandle]
.text:00401649 call [ebx+imports.InternetConnectW]
The resulting value is used to fetch a decrypted string, which in turn is then used as the server name for the InternetConnectW call. The field can also be -1, in these cases the target is skipped:
.text:004015A4 check_target_index:
.text:004015A4 mov [ebp+64h+tar_nr], eax
.text:004015A7 call [ebp+64h+get_field_of_target]
.text:004015AA inc ah
.text:004015AC jz short next_ip
3rd Field - Download Path
The following snippet first reads the third field of a target.
.text:0040167E mov ah, 1
.text:00401680 call [ebp+64h+get_field_of_target]
.text:00401683 mov cl, ah
.text:00401685 call [ebp+64h+get_decrypted_string_by_index]
.text:00401688 push eax
.text:00401689 push esi
.text:0040168A push edi
.text:0040168B call [ebx+imports.HttpOpenRequestW]
The field value is used to reference a decrypted string, which is used as the target of the HttpOpenRequestW call. The third field denotes the url path for the second stage downloads.
4rd Field - Key Index
The fourth field of a target is read in the following snippet. It is used as index into the download keys array:
.text:0040180B mov eax, [ebp+64h+tar_nr]
.text:0040180E mov ah, 2
.text:00401810 call [ebp+64h+get_field_of_target]
.text:00401813 mov cl, ah
.text:00401815 shl ecx, 2
.text:00401818 mov eax, [ebp+64h+download_keys]
In a similar call, the same field is used to index the check keys:
.text:00401857 mov eax, [ebp+64h+tar_nr]
.text:0040185A inc ah
.text:0040185C inc ah
.text:0040185E call [ebp+64h+get_field_of_target]
.text:00401861 mov cl, ah
.text:00401863 shl ecx, 2
.text:00401866 mov eax, [ebp+64h+check_keys]
6th Field - Another Exe Filename
The sixth fields points to a decrypted exe filename. This filename is not used in the my samples — maybe the filename is used by the downloaded payload (which I didn’t analyse).
Purpose of Targets
The first entry in the targets list has a special meaning for all except one sample: it is used to determine the IP address of the victim. All samples with client IP detection used the icanhazip.com website. The remaining targets are used to host the second stage malware.
Observed Config Files
Edit: Added three more samples (June 17th, 2015). This section shows the config files of 10 different samples. The config files were read with the following IDA Pro script:
def print_row(a, b, c=""):
print("{:<15} | {:<40} | {}".format(a, b, c))
def get_keys(ea):
keys = []
nr_keys = Byte(ea)
ea += 1
for i in range(nr_keys):
keys.append(Dword(ea)); ea += 4
return keys, ea
def print_keys(keys, type_):
keys_str = ", ".join(["{:08x}".format(k) for k in keys])
s = "s" if len(keys) > 1 else ""
print_row("{} {} key{}".format(len(keys), type_, s), keys_str)
def get_target_info(target, strings):
id_ = strings[target[0]]
url = "{}{}".format(strings[target[1]], strings[target[2]])
file_ = strings[target[5]]
return url, id_, file_
print_row("field", "value", "comment")
print_row("---", "---", "---")
ea = ScreenEA()
enc = AskYN(1, "are the string encrypted?")
# port
port = Word(ea); ea += 2
# strings
strings = []
s = ""
while Byte(ea) != 1:
b = Byte(ea)
if b and enc:
b ^= 0x13
if not b:
strings.append(s)
s = ""
else:
s += chr(b)
ea += 1
# string infos
print_row("port", port, "range {0}-{1}".format(port, port+3))
print_row("accept-type", "{}, {}".format(strings[3], strings[4]))
print_row("user-agent", strings[6])
print_row("malware name", strings[7], "in %Temp% folder")
print_row("temp file", strings[8], "in %Temp% folder")
# keys
ea += 1
dec_keys, ea = get_keys(ea)
print_keys(dec_keys, "decryption")
check_keys, ea = get_keys(ea)
print_keys(check_keys, "check")
# C2 server
print_row("C2 server", strings[9])
# targets
nr_targets = Byte(ea); ea += 1
print_row("nr of targets", "{}".format(nr_targets))
for k in range(nr_targets):
target = []
for l in range(7):
target.append(Byte(ea)); ea += 1
url, id_, file_= get_target_info(target, strings)
if k == 0:
usage = "client ip"
url = "http://" + url
extra = ""
else:
usage = "download {}".format(k)
url = "https://" + url
extra = "id = {}, file = {}".format(id_, file_)
print_row(usage, url, extra)
All samples were obtained from malwr.com and are shared by the uploader. I use the first eight letters of the hex representation of the MD5 sum as identifier. For each samples I also list the following:
- whether or not the strings are encrypted
- whether the first target is used to determine the client’s IP
- which key-scheduling instruction is used to decrypt downloads. The decryption algorithm is shown in the fourth and last part of this series.
The values after id = denote the root directory used in C2 callbacks. The value after file = is the executable name presumably used by second stage payloads.
Sample 0x7347d213
(This is the sample from this blog post). Sample information:
- MD5
- 7347d2130ab55eac7d6413ee2b515cf1
- string encryption
- yes
- client ip
- yes
- key scheduling
dec
Configuration:
| field | value | comment |
|---|---|---|
| port | 13380 | range 13380-13383 |
| accept-type | text/*, application/* | |
| user-agent | Mozilla/5.0 (Windows NT 6.1; WOW64; rv:37.0) Gecko/20100101 Firefox/37.0 | |
| malware name | wevadez.exe | in %Temp% folder |
| temp file | LogE83.tmp | in %Temp% folder |
| decryption key | 3cb1a338 | |
| check key | 6b5519c2 | |
| C2 server | 91.211.17.201 | |
| nr of targets | 17 | |
| client ip | http://icanhazip.com/ | |
| download 1 | https://95.143.141.50/picc21.png | id = PS21, file = hV.exe |
| download 2 | https://92.38.41.38/picc21.png | id = PS21, file = hV.exe |
| download 3 | https://95.143.130.63/picc21.png | id = PS21, file = hV.exe |
| download 4 | https://95.143.131.160/picc21.png | id = PS21, file = hV.exe |
| download 5 | https://95.143.128.70/picc21.png | id = PS21, file = hV.exe |
| download 6 | https://87.249.149.40/picc21.png | id = PS21, file = hV.exe |
| download 7 | https://195.146.118.46/picc21.png | id = PS21, file = hV.exe |
| download 8 | https://77.48.30.156/picc21.png | id = PS21, file = hV.exe |
| download 9 | https://91.221.217.139/picc21.png | id = PS21, file = hV.exe |
| download 10 | https://77.95.195.68/picc21.png | id = PS21, file = hV.exe |
| download 11 | https://81.90.164.134/picc21.png | id = PS21, file = hV.exe |
| download 12 | https://109.75.154.46/picc21.png | id = PS21, file = hV.exe |
| download 13 | https://95.143.134.103/picc21.png | id = PS21, file = hV.exe |
| download 14 | https://216.245.211.242/picc21.png | id = PS21, file = hV.exe |
| download 15 | https://95.143.131.73/picc21.png | id = PS21, file = hV.exe |
| download 16 | https://95.143.132.118/picc21.png | id = PS21, file = hV.exe |
Sample 0xbda3abd2
Sample information:
- MD5
- bda3abd2f2a632873baee0fb78fd2813
- string encryption
- no
- client ip
- yes
- key scheduling
rol
Configuration:
| field | value | comment |
|---|---|---|
| port | 13068 | range 13068-13071 |
| accept-type | text/*, application/* | |
| user-agent | Mozilla/5.0 (Windows NT 6.1; WOW64; rv:38.0) Gecko/20100101 Firefox/38.0 | |
| malware name | Pisynika.exe | in %Temp% folder |
| temp file | PSC352.tmp | in %Temp% folder |
| decryption key | 523ea087 | |
| check key | 2b2f8604 | |
| C2 server | 188.120.194.101 | |
| nr of targets | 21 | |
| client ip | http://icanhazip.com/ | |
| download 1 | https://69.163.81.211/pictna.png | id = NA, file = AW0.exe |
| download 2 | https://216.254.231.11/pictna.png | id = NA, file = AW0.exe |
| download 3 | https://24.33.131.116/pictna.png | id = NA, file = AW0.exe |
| download 4 | https://68.119.5.32/pictna.png | id = NA, file = AW0.exe |
| download 5 | https://71.194.36.73/pictna.png | id = NA, file = AW0.exe |
| download 6 | https://97.92.125.74/pictna.png | id = NA, file = AW0.exe |
| download 7 | https://98.204.215.92/pictna.png | id = NA, file = AW0.exe |
| download 8 | https://70.121.191.206/pictna.png | id = NA, file = AW0.exe |
| download 9 | https://72.230.82.80/pictna.png | id = NA, file = AW0.exe |
| download 10 | https://178.214.221.89/pictna.png | id = NA, file = AW0.exe |
| download 11 | https://173.248.22.227/pictna.png | id = NA, file = AW0.exe |
| download 12 | https://173.248.31.1/pictna.png | id = NA, file = AW0.exe |
| download 13 | https://173.248.31.6/pictna.png | id = NA, file = AW0.exe |
| download 14 | https://188.255.236.2/pictna.png | id = NA, file = AW0.exe |
| download 15 | https://188.255.167.4/pictna.png | id = NA, file = AW0.exe |
| download 16 | https://173.248.27.163/pictna.png | id = NA, file = AW0.exe |
| download 17 | https://173.243.255.79/pictna.png | id = NA, file = AW0.exe |
| download 18 | https://69.9.204.114/pictna.png | id = NA, file = AW0.exe |
| download 19 | https://73.175.203.173/pictna.png | id = NA, file = AW0.exe |
| download 20 | https://188.255.239.34/pictna.png | id = NA, file = AW0.exe |
Sample 0x95e79d9a
Sample information:
- MD5
- 95e79d9abcc0735d3ce79d75c4cea1ae
- string encryption
- yes
- client ip
- yes
- key scheduling
dec
Configuration:
| field | value | comment |
|---|---|---|
| port | 13176 | range 13176-13179 |
| accept-type | text/, application/ | |
| user-agent | Mozilla/5.0 (Windows NT 6.1; WOW64; rv:37.0) Gecko/20100101 Firefox/37.0 | |
| malware name | nyupodyt.exe | in %Temp% folder |
| temp file | ~DR7892.txt | in %Temp% folder |
| decryption key | 71a588f1 | |
| check key | 4e1a87a9 | |
| C2 server | 93.185.4.90 | |
| nr of targets | 16 | |
| client ip | http://icanhazip.com/ | id = KTA12, file = pBQ.exe |
| download 1 | https://178.214.221.89/kisty12.pdf | id = KTA12, file = pBQ.exe |
| download 2 | https://188.255.142.250/kisty12.pdf | id = KTA12, file = pBQ.exe |
| download 3 | https://37.57.144.177/kisty12.pdf | id = KTA12, file = pBQ.exe |
| download 4 | https://173.248.22.227/kisty12.pdf | id = KTA12, file = pBQ.exe |
| download 5 | https://173.248.31.1/kisty12.pdf | id = KTA12, file = pBQ.exe |
| download 6 | https://173.248.31.6/kisty12.pdf | id = KTA12, file = pBQ.exe |
| download 7 | https://173.248.16.79/kisty12.pdf | id = KTA12, file = pBQ.exe |
| download 8 | https://24.240.107.12/kisty12.pdf | id = KTA12, file = pBQ.exe |
| download 9 | https://173.248.29.213/kisty12.pdf | id = KTA12, file = pBQ.exe |
| download 10 | https://173.248.20.145/kisty12.pdf | id = KTA12, file = pBQ.exe |
| download 11 | https://173.248.27.163/kisty12.pdf | id = KTA12, file = pBQ.exe |
| download 12 | https://173.243.255.79/kisty12.pdf | id = KTA12, file = pBQ.exe |
| download 13 | https://69.9.204.114/kisty12.pdf | id = KTA12, file = pBQ.exe |
| download 14 | https://73.175.203.173/kisty12.pdf | id = KTA12, file = pBQ.exe |
| download 15 | https://38.124.72.224/kisty12.pdf | id = KTA12, file = pBQ.exe |
Sample 0x457f0283
Sample information:
- MD5
- 457f0283c17b00b29e335829f6a716fd
- string encryption
- no
- client ip
- yes
- key scheduling
rol
Configuration:
| field | value | comment |
|---|---|---|
| port | 13068 | range 13068-13071 |
| accept-type | text/*, application/* | |
| user-agent | Mozilla/5.0 (Windows NT 6.1) AppleWebKit/536.36 (KHTML, like Gecko) Chrome/42.0.2357.81 Safari/536.36 | |
| malware name | uticopfull.exe | in %Temp% folder |
| temp file | UticopSetup.log | in %Temp% folder |
| decryption key | 2B415B20 | |
| check key | 64FDFF57 | |
| C2 server | 188.120.194.101 | |
| nr of targets | 16 | |
| client ip | http://icanhazip.com/ | |
| download 1 | 216.51.193.145/taser4.png | id = SALE4, file = xD8.exe |
| download 2 | 96.46.103.232/taser4.png | id = SALE4, file = xD8.exe |
| download 3 | 68.70.242.203/taser4.png | id = SALE4, file = xD8.exe |
| download 4 | 66.215.30.118/taser4.png | id = SALE4, file = xD8.exe |
| download 5 | 107.161.207.151/taser4.png | id = SALE4, file = xD8.exe |
| download 6 | 31.131.142.204/taser4.png | id = SALE4, file = xD8.exe |
| download 7 | 96.46.99.183/taser4.png | id = SALE4, file = xD8.exe |
| download 8 | 188.255.175.252/taser4.png | id = SALE4, file = xD8.exe |
| download 9 | 96.46.100.49/taser4.png | id = SALE4, file = xD8.exe |
| download 10 | 64.111.36.52/taser4.png | id = SALE4, file = xD8.exe |
| download 11 | 38.124.74.146/taser4.png | id = SALE4, file = xD8.exe |
| download 12 | 38.124.69.206/taser4.png | id = SALE4, file = xD8.exe |
| download 13 | 38.124.174.66/taser4.png | id = SALE4, file = xD8.exe |
| download 14 | 38.124.74.146/taser4.png | id = SALE4, file = xD8.exe |
| download 15 | 38.124.174.213/taser4.png | id = SALE4, file = xD8.exe |
Sample 0x105beb32
Sample information:
- MD5
- 105beb3223cbff3641cbe881bc4fbf45
- string encryption
- yes
- client ip
- yes
- key scheduling
rol
Configuration:
| field | value | comment |
|---|---|---|
| port | 13100 | range 13100-13103 |
| accept-type | text/*, application/* | |
| user-agent | Mozilla/5.0 (Windows NT 6.1) AppleWebKit/538.37 (KHTML, like Gecko) Chrome/44.0.2457.82 Safari/538.37 | |
| malware name | Mivinad.exe | in %Temp% folder |
| temp file | Mivi-738.log | in %Temp% folder |
| decryption key | 3e51cf28 | |
| check key | 74090789 | |
| C2 server | 188.120.194.101 | |
| nr of targets | 20 | |
| client ip | http://icanhazip.com/ | |
| download 1 | https://78.32.124.231/j11.zip | id = AMG11, file = lL8.exe |
| download 2 | https://76.105.248.137/j11.zip | id = AMG11, file = lL8.exe |
| download 3 | https://75.132.173.27/j11.zip | id = AMG11, file = lL8.exe |
| download 4 | https://76.84.81.120/j11.zip | id = AMG11, file = lL8.exe |
| download 5 | https://76.28.92.4/j11.zip | id = AMG11, file = lL8.exe |
| download 6 | https://65.74.106.143/j11.zip | id = AMG11, file = lL8.exe |
| download 7 | https://66.191.25.136/j11.zip | id = AMG11, file = lL8.exe |
| download 8 | https://98.222.64.184/j11.zip | id = AMG11, file = lL8.exe |
| download 9 | https://69.144.171.44/j11.zip | id = AMG11, file = lL8.exe |
| download 10 | https://65.33.236.173/j11.zip | id = AMG11, file = lL8.exe |
| download 11 | https://66.227.223.219/j11.zip | id = AMG11, file = lL8.exe |
| download 12 | https://96.37.204.12/j11.zip | id = AMG11, file = lL8.exe |
| download 13 | https://66.196.63.33/j11.zip | id = AMG11, file = lL8.exe |
| download 14 | https://69.142.124.76/j11.zip | id = AMG11, file = lL8.exe |
| download 15 | https://216.16.93.250/j11.zip | id = AMG11, file = lL8.exe |
| download 16 | https://24.19.25.40/j11.zip | id = AMG11, file = lL8.exe |
| download 17 | https://98.246.210.27/j11.zip | id = AMG11, file = lL8.exe |
| download 18 | https://66.196.61.218/j11.zip | id = AMG11, file = lL8.exe |
| download 19 | https://71.99.130.24/j11.zip | id = AMG11, file = lL8.exe |
Sample 0x8d00dfdc
Sample information:
- MD5
- 8d00dfdc4d7932b8db5322ce439cd44b
- string encryption
- no
- client ip
- yes
- key scheduling
rol
Configuration:
| field | value | comment |
|---|---|---|
| port | 13096 | range 13096-13099 |
| accept-type | text/*, application/* | |
| user-agent | Mozilla/5.0 (Windows NT 6.1) AppleWebKit/538.37 (KHTML, like Gecko) Chrome/44.0.2457.82 Safari/538.37 | |
| malware name | Gycijaba.exe | in %Temp% folder |
| temp file | Gyci7EC9.txt | in %Temp% folder |
| decryption key | 3e51cf28 | |
| check key | 74090789 | |
| C2 server | 188.120.194.101 | |
| nr of targets | 20 | |
| client ip | http://icanhazip.com/ | |
| download 1 | https://78.32.124.231/ua.png | id = UAM, file = Ner5.exe |
| download 2 | https://76.105.248.137/ua.png | id = UAM, file = Ner5.exe |
| download 3 | https://75.132.173.27/ua.png | id = UAM, file = Ner5.exe |
| download 4 | https://76.84.81.120/ua.png | id = UAM, file = Ner5.exe |
| download 5 | https://76.28.92.4/ua.png | id = UAM, file = Ner5.exe |
| download 6 | https://65.74.106.143/ua.png | id = UAM, file = Ner5.exe |
| download 7 | https://66.191.25.136/ua.png | id = UAM, file = Ner5.exe |
| download 8 | https://98.222.64.184/ua.png | id = UAM, file = Ner5.exe |
| download 9 | https://69.144.171.44/ua.png | id = UAM, file = Ner5.exe |
| download 10 | https://65.33.236.173/ua.png | id = UAM, file = Ner5.exe |
| download 11 | https://66.227.223.219/ua.png | id = UAM, file = Ner5.exe |
| download 12 | https://96.37.204.12/ua.png | id = UAM, file = Ner5.exe |
| download 13 | https://66.196.63.33/ua.png | id = UAM, file = Ner5.exe |
| download 14 | https://69.142.124.76/ua.png | id = UAM, file = Ner5.exe |
| download 15 | https://216.16.93.250/ua.png | id = UAM, file = Ner5.exe |
| download 16 | https://24.19.25.40/ua.png | id = UAM, file = Ner5.exe |
| download 17 | https://98.246.210.27/ua.png | id = UAM, file = Ner5.exe |
| download 18 | https://66.196.61.218/ua.png | id = UAM, file = Ner5.exe |
| download 19 | https://71.99.130.24/ua.png | id = UAM, file = Ner5.exe |
Sample 0x98b126f5
Sample information:
- MD5
- 98b126f52ca20fd89eafceed795cee15
- string encryption
- no
- client ip
- no
- key scheduling
inc
Configuration:
| field | value | comment |
|---|---|---|
| port | 41300 | range 41300-41303 |
| accept-type | text/, application/ | |
| user-agent | Mazilla/4.0 | |
| malware name | mscodecs.exe | in %Temp% folder |
| temp file | auat498.tmp | in %Temp% folder |
| decryption key | 33c13e3c | |
| check key | 74e7fc60 | |
| C2 server | 202.153.35.133 | |
| nr of targets | 2 | |
| download 1 | http://photolife.ir/logfiles/doc_ku11.pdf | id = 2301uk11, file = cOFrcJtt.exe |
| download 2 | https://carrozzeriavolta.com/mandoc/doc_ku11.pdf | id = 2301uk11, file = cOFrcJtt.exe |
Sample 0x07ea0d7c
Sample information:
- MD5
- 07ea0d7c04af3520da43f38ef8211aa8
- string encryption
- no
- client ip
- yes
- key scheduling
dec- method
- this sample uses the simplified payload format without decryption keys and temp file name.
Configuration:
| field | value | comment |
|---|---|---|
| port | 13164 | range 13164-13167 |
| accept-type | text/, application/ | |
| user-agent | Mozilla/5.0 (Windows NT 6.1) AppleWebKit/538.37 (KHTML, like Gecko) Chrome/44.0.2457.82 Safari/538.37 | |
| malware name | razacer.exe | in %Temp% folder |
| decryption key | 55c28387 | |
| C2 server | 188.120.194.101 | |
| nr of targets | 51 | |
| client ip | http://icanhazip.com/ | id = Img12, file = eprath.exe |
| download 1 | https://173.248.29.43/im12.png | id = Img12, file = eprath.exe |
| download 2 | https://109.86.226.85/im12.png | id = Img12, file = eprath.exe |
| download 3 | https://24.220.92.193/im12.png | id = Img12, file = eprath.exe |
| download 4 | https://176.36.251.208/im12.png | id = Img12, file = eprath.exe |
| download 5 | https://188.255.165.154/im12.png | id = Img12, file = eprath.exe |
| download 6 | https://173.216.240.56/im12.png | id = Img12, file = eprath.exe |
| download 7 | https://68.190.246.142/im12.png | id = Img12, file = eprath.exe |
| download 8 | https://188.255.169.176/im12.png | id = Img12, file = eprath.exe |
| download 9 | https://75.137.112.81/im12.png | id = Img12, file = eprath.exe |
| download 10 | https://69.163.81.211/im12.png | id = Img12, file = eprath.exe |
| download 11 | https://216.254.231.11/im12.png | id = Img12, file = eprath.exe |
| download 12 | https://24.33.131.116/im12.png | id = Img12, file = eprath.exe |
| download 13 | https://68.119.5.32/im12.png | id = Img12, file = eprath.exe |
| download 14 | https://97.92.125.74/im12.png | id = Img12, file = eprath.exe |
| download 15 | https://98.204.215.92/im12.png | id = Img12, file = eprath.exe |
| download 16 | https://72.230.82.80/im12.png | id = Img12, file = eprath.exe |
| download 17 | https://208.123.130.173/im12.png | id = Img12, file = eprath.exe |
| download 18 | https://178.214.221.89/im12.png | id = Img12, file = eprath.exe |
| download 19 | https://173.248.22.227/im12.png | id = Img12, file = eprath.exe |
| download 20 | https://173.248.31.1/im12.png | id = Img12, file = eprath.exe |
| download 21 | https://173.248.31.6/im12.png | id = Img12, file = eprath.exe |
| download 22 | https://173.248.27.163/im12.png | id = Img12, file = eprath.exe |
| download 23 | https://173.243.255.79/im12.png | id = Img12, file = eprath.exe |
| download 24 | https://69.9.204.114/im12.png | id = Img12, file = eprath.exe |
| download 25 | https://73.175.203.173/im12.png | id = Img12, file = eprath.exe |
| download 26 | https://188.255.239.34/im12.png | id = Img12, file = eprath.exe |
| download 27 | https://75.132.173.27/im12.png | id = Img12, file = eprath.exe |
| download 28 | https://76.28.92.4/im12.png | id = Img12, file = eprath.exe |
| download 29 | https://71.194.36.73/im12.png | id = Img12, file = eprath.exe |
| download 30 | https://98.222.64.184/im12.png | id = Img12, file = eprath.exe |
| download 31 | https://69.144.171.44/im12.png | id = Img12, file = eprath.exe |
| download 32 | https://65.33.236.173/im12.png | id = Img12, file = eprath.exe |
| download 33 | https://66.227.223.219/im12.png | id = Img12, file = eprath.exe |
| download 34 | https://96.37.204.12/im12.png | id = Img12, file = eprath.exe |
| download 35 | https://66.196.63.33/im12.png | id = Img12, file = eprath.exe |
| download 36 | https://71.99.130.24/im12.png | id = Img12, file = eprath.exe |
| download 37 | https://216.16.93.250/im12.png | id = Img12, file = eprath.exe |
| download 38 | https://24.19.25.40/im12.png | id = Img12, file = eprath.exe |
| download 39 | https://98.246.210.27/im12.png | id = Img12, file = eprath.exe |
| download 40 | https://66.196.61.218/im12.png | id = Img12, file = eprath.exe |
| download 41 | https://69.180.128.71/im12.png | id = Img12, file = eprath.exe |
| download 42 | https://98.214.11.253/im12.png | id = Img12, file = eprath.exe |
| download 43 | https://24.148.217.188/im12.png | id = Img12, file = eprath.exe |
| download 44 | https://98.209.75.164/im12.png | id = Img12, file = eprath.exe |
| download 45 | https://76.105.248.137/im12.png | id = Img12, file = eprath.exe |
| download 46 | https://67.239.210.131/im12.png | id = Img12, file = eprath.exe |
| download 47 | https://173.216.247.74/im12.png | id = Img12, file = eprath.exe |
| download 48 | https://64.111.36.35/im12.png | id = Img12, file = eprath.exe |
| download 49 | https://69.9.204.16/im12.png | id = Img12, file = eprath.exe |
| download 50 | https://77.48.30.156/im12.png | id = Img12, file = eprath.exe |
Sample 0x7422731b
Sample information:
- MD5
- 7422731bbe817e85dbac70f3f98243b6
- string encryption
- yes
- client ip
- yes
- key scheduling
dec- method
- this sample uses the simplified payload format without decryption keys and temp file name.
| field | value | comment |
|---|---|---|
| port | 13140 | range 13140-13143 |
| accept-type | text/, application/ | |
| user-agent | Mozilla/5.0 (Windows NT 6.1; WOW64; rv:38.0) Gecko/20100101 Firefox/38.0 | |
| malware name | bijaweed.exe | in %Temp% folder |
| decryption key | 27185cd3 | |
| C2 server | 188.120.194.101 | |
| nr of targets | 53 | |
| client ip | http://icanhazip.com/ | id = Tos21, file = uxajake.exe |
| download 1 | https://173.248.29.43/tos21.zip | id = Tos21, file = uxajake.exe |
| download 2 | https://109.86.226.85/tos21.zip | id = Tos21, file = uxajake.exe |
| download 3 | https://24.220.92.193/tos21.zip | id = Tos21, file = uxajake.exe |
| download 4 | https://176.36.251.208/tos21.zip | id = Tos21, file = uxajake.exe |
| download 5 | https://188.255.165.154/tos21.zip | id = Tos21, file = uxajake.exe |
| download 6 | https://173.216.240.56/tos21.zip | id = Tos21, file = uxajake.exe |
| download 7 | https://68.190.246.142/tos21.zip | id = Tos21, file = uxajake.exe |
| download 8 | https://188.255.169.176/tos21.zip | id = Tos21, file = uxajake.exe |
| download 9 | https://162.255.126.8/tos21.zip | id = Tos21, file = uxajake.exe |
| download 10 | https://75.137.112.81/tos21.zip | id = Tos21, file = uxajake.exe |
| download 11 | https://69.163.81.211/tos21.zip | id = Tos21, file = uxajake.exe |
| download 12 | https://216.254.231.11/tos21.zip | id = Tos21, file = uxajake.exe |
| download 13 | https://24.33.131.116/tos21.zip | id = Tos21, file = uxajake.exe |
| download 14 | https://68.119.5.32/tos21.zip | id = Tos21, file = uxajake.exe |
| download 15 | https://71.194.36.73/tos21.zip | id = Tos21, file = uxajake.exe |
| download 16 | https://97.92.125.74/tos21.zip | id = Tos21, file = uxajake.exe |
| download 17 | https://98.204.215.92/tos21.zip | id = Tos21, file = uxajake.exe |
| download 18 | https://72.230.82.80/tos21.zip | id = Tos21, file = uxajake.exe |
| download 19 | https://208.123.130.173/tos21.zip | id = Tos21, file = uxajake.exe |
| download 20 | https://178.214.221.89/tos21.zip | id = Tos21, file = uxajake.exe |
| download 21 | https://173.248.22.227/tos21.zip | id = Tos21, file = uxajake.exe |
| download 22 | https://173.248.31.1/tos21.zip | id = Tos21, file = uxajake.exe |
| download 23 | https://173.248.31.6/tos21.zip | id = Tos21, file = uxajake.exe |
| download 24 | https://173.248.27.163/tos21.zip | id = Tos21, file = uxajake.exe |
| download 25 | https://173.243.255.79/tos21.zip | id = Tos21, file = uxajake.exe |
| download 26 | https://69.9.204.114/tos21.zip | id = Tos21, file = uxajake.exe |
| download 27 | https://73.175.203.173/tos21.zip | id = Tos21, file = uxajake.exe |
| download 28 | https://188.255.239.34/tos21.zip | id = Tos21, file = uxajake.exe |
| download 29 | https://75.132.173.27/tos21.zip | id = Tos21, file = uxajake.exe |
| download 30 | https://76.84.81.120/tos21.zip | id = Tos21, file = uxajake.exe |
| download 31 | https://76.28.92.4/tos21.zip | id = Tos21, file = uxajake.exe |
| download 32 | https://65.74.106.143/tos21.zip | id = Tos21, file = uxajake.exe |
| download 33 | https://98.222.64.184/tos21.zip | id = Tos21, file = uxajake.exe |
| download 34 | https://69.144.171.44/tos21.zip | id = Tos21, file = uxajake.exe |
| download 35 | https://65.33.236.173/tos21.zip | id = Tos21, file = uxajake.exe |
| download 36 | https://66.227.223.219/tos21.zip | id = Tos21, file = uxajake.exe |
| download 37 | https://96.37.204.12/tos21.zip | id = Tos21, file = uxajake.exe |
| download 38 | https://66.196.63.33/tos21.zip | id = Tos21, file = uxajake.exe |
| download 39 | https://71.99.130.24/tos21.zip | id = Tos21, file = uxajake.exe |
| download 40 | https://216.16.93.250/tos21.zip | id = Tos21, file = uxajake.exe |
| download 41 | https://24.19.25.40/tos21.zip | id = Tos21, file = uxajake.exe |
| download 42 | https://98.246.210.27/tos21.zip | id = Tos21, file = uxajake.exe |
| download 43 | https://66.196.61.218/tos21.zip | id = Tos21, file = uxajake.exe |
| download 44 | https://69.180.128.71/tos21.zip | id = Tos21, file = uxajake.exe |
| download 45 | https://98.214.11.253/tos21.zip | id = Tos21, file = uxajake.exe |
| download 46 | https://24.148.217.188/tos21.zip | id = Tos21, file = uxajake.exe |
| download 47 | https://98.209.75.164/tos21.zip | id = Tos21, file = uxajake.exe |
| download 48 | https://76.105.248.137/tos21.zip | id = Tos21, file = uxajake.exe |
| download 49 | https://67.239.210.131/tos21.zip | id = Tos21, file = uxajake.exe |
| download 50 | https://173.216.247.74/tos21.zip | id = Tos21, file = uxajake.exe |
| download 51 | https://64.111.36.35/tos21.zip | id = Tos21, file = uxajake.exe |
| download 52 | https://69.9.204.16/tos21.zip | id = Tos21, file = uxajake.exe |
Sample 0x846cb698
Sample information:
- MD5
- 846cb6984114499978d4fe29b5f5afa7
- string encryption
- no
- client ip
- yes
- key scheduling
rol
| field | value | comment |
|---|---|---|
| port | 13152 | range 13152-13155 |
| accept-type | text/, application/ | |
| user-agent | Mozilla/5.0 (Windows NT 6.1; WOW64; rv:36.0) Gecko/20100101 Firefox/36.0 | |
| malware name | fihatyka.exe | in %Temp% folder |
| temp file | FIH_244D.log | in %Temp% folder |
| decryption key | 5b244d31 | |
| check key | 0250f3d8 | |
| C2 server | 188.120.194.101 | |
| nr of targets | 51 | |
| client ip | http://icanhazip.com/ | id = 211, file = QZP1.exe |
| download 1 | https://173.248.29.43/f2011.zip | id = 211, file = QZP1.exe |
| download 2 | https://109.86.226.85/f2011.zip | id = 211, file = QZP1.exe |
| download 3 | https://24.220.92.193/f2011.zip | id = 211, file = QZP1.exe |
| download 4 | https://176.36.251.208/f2011.zip | id = 211, file = QZP1.exe |
| download 5 | https://188.255.165.154/f2011.zip | id = 211, file = QZP1.exe |
| download 6 | https://173.216.240.56/f2011.zip | id = 211, file = QZP1.exe |
| download 7 | https://68.190.246.142/f2011.zip | id = 211, file = QZP1.exe |
| download 8 | https://188.255.169.176/f2011.zip | id = 211, file = QZP1.exe |
| download 9 | https://75.137.112.81/f2011.zip | id = 211, file = QZP1.exe |
| download 10 | https://69.163.81.211/f2011.zip | id = 211, file = QZP1.exe |
| download 11 | https://216.254.231.11/f2011.zip | id = 211, file = QZP1.exe |
| download 12 | https://24.33.131.116/f2011.zip | id = 211, file = QZP1.exe |
| download 13 | https://68.119.5.32/f2011.zip | id = 211, file = QZP1.exe |
| download 14 | https://97.92.125.74/f2011.zip | id = 211, file = QZP1.exe |
| download 15 | https://98.204.215.92/f2011.zip | id = 211, file = QZP1.exe |
| download 16 | https://72.230.82.80/f2011.zip | id = 211, file = QZP1.exe |
| download 17 | https://208.123.130.173/f2011.zip | id = 211, file = QZP1.exe |
| download 18 | https://178.214.221.89/f2011.zip | id = 211, file = QZP1.exe |
| download 19 | https://173.248.22.227/f2011.zip | id = 211, file = QZP1.exe |
| download 20 | https://173.248.31.1/f2011.zip | id = 211, file = QZP1.exe |
| download 21 | https://173.248.31.6/f2011.zip | id = 211, file = QZP1.exe |
| download 22 | https://173.248.27.163/f2011.zip | id = 211, file = QZP1.exe |
| download 23 | https://173.243.255.79/f2011.zip | id = 211, file = QZP1.exe |
| download 24 | https://69.9.204.114/f2011.zip | id = 211, file = QZP1.exe |
| download 25 | https://73.175.203.173/f2011.zip | id = 211, file = QZP1.exe |
| download 26 | https://188.255.239.34/f2011.zip | id = 211, file = QZP1.exe |
| download 27 | https://75.132.173.27/f2011.zip | id = 211, file = QZP1.exe |
| download 28 | https://76.28.92.4/f2011.zip | id = 211, file = QZP1.exe |
| download 29 | https://71.194.36.73/f2011.zip | id = 211, file = QZP1.exe |
| download 30 | https://98.222.64.184/f2011.zip | id = 211, file = QZP1.exe |
| download 31 | https://69.144.171.44/f2011.zip | id = 211, file = QZP1.exe |
| download 32 | https://65.33.236.173/f2011.zip | id = 211, file = QZP1.exe |
| download 33 | https://66.227.223.219/f2011.zip | id = 211, file = QZP1.exe |
| download 34 | https://96.37.204.12/f2011.zip | id = 211, file = QZP1.exe |
| download 35 | https://66.196.63.33/f2011.zip | id = 211, file = QZP1.exe |
| download 36 | https://71.99.130.24/f2011.zip | id = 211, file = QZP1.exe |
| download 37 | https://216.16.93.250/f2011.zip | id = 211, file = QZP1.exe |
| download 38 | https://24.19.25.40/f2011.zip | id = 211, file = QZP1.exe |
| download 39 | https://98.246.210.27/f2011.zip | id = 211, file = QZP1.exe |
| download 40 | https://66.196.61.218/f2011.zip | id = 211, file = QZP1.exe |
| download 41 | https://69.180.128.71/f2011.zip | id = 211, file = QZP1.exe |
| download 42 | https://98.214.11.253/f2011.zip | id = 211, file = QZP1.exe |
| download 43 | https://24.148.217.188/f2011.zip | id = 211, file = QZP1.exe |
| download 44 | https://98.209.75.164/f2011.zip | id = 211, file = QZP1.exe |
| download 45 | https://76.105.248.137/f2011.zip | id = 211, file = QZP1.exe |
| download 46 | https://67.239.210.131/f2011.zip | id = 211, file = QZP1.exe |
| download 47 | https://173.216.247.74/f2011.zip | id = 211, file = QZP1.exe |
| download 48 | https://64.111.36.35/f2011.zip | id = 211, file = QZP1.exe |
| download 49 | https://69.9.204.16/f2011.zip | id = 211, file = QZP1.exe |
| download 50 | https://77.48.30.156/f2011.zip | id = 211, file = QZP1.exe |
